miui bitcoin

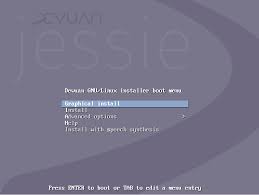
Mucho se ha hablado en las últimas semanas de los parecidos 'demasiado razonables' que Mi (Xiaomi) tiene con Apple.Su último evento de presentación del Mi 4 fue especialmente significativo en ese apartado, y de hecho la empresa utilizó una diapositiva con el famoso "One more thing" de las presentaciones de Steve Jobs para anunciar un último apartado en el evento.Ahora esas comparaciones vuelven a la palestra tras la salida a escena de MIUI v6, la nueva versión de la ROM de Mi derivada de Android.En esta última edición tanto las tipografías como los iconos y el resto de elementos visuales recuerdan mucho al diseño de la interfaz de iOS 7 que hizo su debut el año pasado.Aún así hay por supuesto elementos que son suficientemente diferenciadores, como un nuevo sistema de presentación de notificaciones que se muestran en una barra de mayor tamaño en la parte superior de la pantalla.Además la flexibilidad es mayor y en notificaciones entrantes (por ejemplo al recibir una llamada mientras hacemos una foto) ese aviso ocupará una parte mínima de la pantalla.

La pantalla de bloqueo también dispone de un acceso directo a las notificaciones, y un indicador numérico permite conocer el númeor de notificaciones sin leer que tenemos en nuestra "bandeja" de notificaciones.Otras novedades afectan a la nueva interfaz de llamadas que no solo identificará al contacto que nos llama a través de nuestra propia agenda, sino que incluso es capaz de identificar números que no tenemos guardados.Para ello en Xiaomi indican que tienen una base de datos con 60 millones de números de telefonos de empresas guardados, lo que permite que se identifiquen parte de las llamadas que recibimos y de las que no tenemos guardado el contacto.
bitcoin rolf leuenbergerEs más que probable que esa base de datos esté totalmente centrada en China, no obstante.
bitcoin lernenAlgunas aplicaciones también han sufrido cambios importantes en la interfaz, como sucede con la aplicación de correo electrónico (Mail) o la que nos permite sacar fotos, que por ejemplo hace uso del gesto de deslizar el dedo hacia abajo para intercambiar entre la cámara frontal y la trasera.
trace mayer bitcoin
La nueva ROM ya está traducida a 28 idiomas, y hay 26 versiones localizadas en otros tantos países del sitio web oficial de MIUI, algo que vuelve a demostrar el interés por una ROM que acaba adaptándose a otros muchos dispositivos a pesar de estar orientada originalmente a los smartphones de esta compañía.MIUI 6 está disponible inicialmente para 1.000 beta-testers, que en una semana serán 10.000.La empresa ofrecerá una versión para desarrolladores a principios de septiembre, y en octubre (sin día fijo) ofrecerá por fin la versión final y pública de su ROM.Vía | TheTecholic Más información | Mi (Facebook) En Xataka | Apple presenta iOS 7Not everyone thinks Segways are funny.Beijing-based competitor Ninebot just bought Bedford, N.H.-based Segway, the electric two-wheeled personal transportation vehicle.Terms of the deal were not made public, but in addition to the acquisition, Ninebot did say that it has received an $80 million cash injection from investment houses MIUI Technology, Sequoia Capital, Sunwei Fund and Sequoia Capital.After the acquisition, Segway and Ninebot will continue to operate as their own brands.

The first Segway came out in 2001 and was invented by Dean Kamen.At the time, hopes were high that the personal transportation vehicle would be a blowout success.With a price tag well above $3,000 -- out of reach for the everyday consumer who was find getting around on foot anyway -- along with a design that earned it an awkward reputation, the Segway was largely considered a fail.(Speaking of fails -- if you haven’t ever seen any of the Segway blooper videos on YouTube, here’s one.)Related: Driverless Cars Won't Make Roadways Perfectly SafeStill, Segway has 250 distribution points in 80 countries.And that’s something to take seriously.Being under one umbrella now, Segway and Ninebot will share technology and research notes.“It creates a development opportunity for the short-distance transportation industry, which the combined company will lead by widely applying a series of technologies, such as electric driving, mobile internet and human-computer interaction, on future products,” said Lufeng Gao, founder and CEO of Ninebot, in a statement.Founded in 2012, Ninebot makes two-wheeled electric vehicles similar to the Segway as well as one-wheeled unicycles.

Oddly enough, it was one of the companies accused of patent infringement by Segway last year.Related: Elon Musk: Human-Driven Cars Might Someday Be BannedPwned websites Breached websites that have been loaded into this service Here's an overview of the various breaches that have been consolidated into this site.Each of these has been dumped publicly and is readily available via various sites on the web.This information is also available via an RSS feed.Exploit.In Anti Public Combo List River City Media Spam List MySpace NetEase LinkedIn Adobe Badoo VK Youku Rambler Dropbox tumblr Modern Business Solutions Zoosk iMesh Edmodo Fling Last.fm NetProspex SC Daily Phone Spam List Ashley Madison Special K Data Feed Spam List Evony Tianya Neopets QIP GFAN R2Games Taobao 000webhost Cross Fire Gamigo Data Enrichment Records Heroes of Newerth Civil Online uuu9 Experian Lifeboat 126 xat Nexus Mods Leet Пара Па QuinStreet VTech Dump Bitcoin Security Forum Gmail Dump Snapchat Money Bookers 17 Adult Friend Finder Trillian Neteller Спрашивай.ру InterPals DLH.net MPGH XSplit Uiggy Funimation iPmart ClixSense FashionFantasyGame Patreon Wishbone Bell (2017 breach) i-Dressup gPotato GameTuts CD Projekt RED Flash Flash Revolution Nihonomaru Ster-Kinekor Dungeons & Dragons Online Nival Army Force Online Aternos Naughty America Eroticy YouPorn Xbox 360 ISO Elance PSP ISO Fur Affinity Gawker Gamerzplanet NextGenUpdate Yandex Dump Lord of the Rings Online DaniWeb Beautiful People Lookbook GeekedIn Forbes R2 (2017 forum breach) War Inc.

HongFire Little Monsters CrimeAgency vBulletin Hacks OwnedCore MoDaCo Stratfor Manga Traders Pokémon Negro Warframe Onverse Brazzers Black Hat World Abandonia Android Forums WildStar mSpy Pokébip Domino's DaFont Final Fantasy Shrine Comcast ThisHabbo Forum HLTV Nulled Paddy Power CloudPets BTC-E Battlefield Heroes Unreal Engine vBulletin Kimsufi Bitcoin Talk WIIU ISO Yahoo OVH PS3Hax Team SoloMid Xbox-Scene Avast PayAsUGym VINs uTorrent Freedom Hosting II MrExcel Torrent Invites PSX-Scene Plex Health Now Networks Sumo Torrent Seedpeer MajorGeeks myRepoSpace Foxy Bingo Epic Games Bot of Legends COMELEC (Philippines Voters) Win7Vista Forum GTAGaming hackforums.net Minefield Heroes of Gaia The Fappening The Candid Board PHP Freaks Boxee Muslim Match WPT Amateur Poker League Linux Mint StarNet WHMCS Soundwave SkTorrent Pokémon Creed Malwarebytes Telecom Regulatory Authority of India Rosebutt Board Regpack Insanelyi Teracod Mac-Torrents Qatar National Bank TruckersMP eThekwini Municipality Non Nude Girls ServerPact Retina-X Minecraft World Map Vodafone Spirol Quantum Booter Hemmakväll Lounge Board Flashback Pixel Federation Muslim Directory Sony BigMoneyJobs Fridae BitTorrent Hacking Team Business Acumen Magazine Bell (2014 breach) MyVidster Crack Community Verified Ethereum Minecraft Pocket Edition Forum Lizard Squad Astropid UN Internet Governance Forum Tesco Sensitive breach, not publicly searchable Retired breach, removed from system Unverified breach, may be sourced from elsewhere Fabricated breach, likely not legitimate Spam List, used for spam marketing 000webhost In approximately March 2015, the free web hosting provider 000webhost suffered a major data breach that exposed over 13 million customer records.

The data was sold and traded before 000webhost was alerted in October.The breach included names, email addresses and plain text passwords.Compromised data: Email addresses, IP addresses, Names, Passwords 126 In approximately 2012, it's alleged that the Chinese email service known as 126 suffered a data breach that impacted 6.4 million subscribers.Whilst there is evidence that the data is legitimate, due to the difficulty of emphatically verifying the Chinese breach it has been flagged as "unverified".The data in the breach contains email addresses and plain text passwords.Read more about Chinese data breaches in Have I been pwned.Compromised data: Email addresses, Passwords 17 In April 2016, customer data obtained from the streaming app known as "17" appeared listed for sale on a Tor hidden service marketplace.The data contained over 4 million unique email addresses along with IP addresses, usernames and passwords stored as unsalted MD5 hashes.Compromised data: Device information, Email addresses, IP addresses, Passwords, Usernames Abandonia In November 2015, the gaming website dedicated to classic DOS games Abandonia suffered a data breach resulting in the exposure of 776k unique user records.

The data contained email and IP addresses, usernames and salted MD5 hashes of passwords.Compromised data: Email addresses, IP addresses, Passwords, Usernames suffered a data breach that exposed over 430k forum members' accounts.The data was being actively traded on underground forums and included email addresses, birth dates and passwords.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames Adobe In October 2013, 153 million Adobe accounts were breached with each containing an internal ID, username, email, encrypted password and a password hint in plain text.The password cryptography was poorly done and many were quickly resolved back to plain text.The unencrypted hints also disclosed much about the passwords adding further to the risk that hundreds of millions of Adobe customers already faced.Compromised data: Email addresses, Password hints, Passwords, Usernames Adult Friend Finder In May 2015, the adult hookup site Adult Friend Finder was hacked and nearly 4 million records dumped publicly.

The data dump included extremely sensitive personal information about individuals and their relationship statuses and sexual preferences combined with personally identifiable information.Compromised data: Dates of birth, Email addresses, Genders, Geographic locations, IP addresses, Races, Relationship statuses, Sexual orientations, Spoken languages, Usernames suffered a breach which resulted in more than 180k user accounts being published publicly.The breach included a raft of personal information on registered users plus despite assertions of not distributing personally identifiable information, the site also leaked the IP addresses used by the registered identities.Compromised data: Email addresses, Genders, Geographic locations, IP addresses, Passwords, Usernames, Website activity, Years of birth and containing 6.5M accounts was leaked online.The data in the breach contains email addresses and MD5 password hashes.Compromised data: Email addresses, Passwords Android Forums In October 2011, the Android Forums website was hacked and 745k user accounts were subsequently leaked publicly.

The compromised data included email addresses, user birth dates and passwords stored as a salted MD5 hash.Compromised data: Dates of birth, Email addresses, Homepage URLs, Instant messenger identities, IP addresses, Passwords Anti Public Combo List In December 2016, a huge list of email address and password pairs appeared in a "combo list" referred to as "Anti Public".The list contained 458 million unique email addresses, many with multiple different passwords hacked from various online systems.The list was broadly circulated and used for "credential stuffing", that is attackers employ it in an attempt to identify other online systems where the account owner had reused their password.For detailed background on this incident, read Password reuse, credential stuffing and another billion records in Have I been pwned.Compromised data: Email addresses, Passwords Army Force Online In May 2016, the the online gaming site Army Force Online suffered a data breach that exposed 1.5M accounts.

The breached data was found being regularly traded online and included usernames, email and IP addresses and MD5 passwords.Compromised data: Avatars, Email addresses, Geographic locations, IP addresses, Names, Passwords, Usernames, Website activity Ashley Madison In July 2015, the infidelity website Ashley Madison suffered a serious data breach.The attackers threatened Ashley Madison with the full disclosure of the breach unless the service was shut down.One month later, the database was dumped including more than 30M unique email addresses.This breach has been classed as "sensitive" and is not publicly searchable, although individuals may discover if they've been impacted by registering for notifications.Read about this approach in detail.Compromised data: Dates of birth, Email addresses, Ethnicities, Genders, Names, Passwords, Payment histories, Phone numbers, Physical addresses, Security questions and answers, Sexual orientations, Usernames, Website activity Astropid In December 2013, the vBulletin forum for the social engineering site known as "AstroPID" was breached and leaked publicly.

The site provided tips on fraudulently obtaining goods and services, often by providing a legitimate "PID" or Product Information Description.The breach resulted in nearly 6k user accounts and over 220k private messages between forum members being exposed.Compromised data: Email addresses, Instant messenger identities, IP addresses, Names, Passwords, Private messages, Usernames, Website activity Aternos In December 2015, the service for creating and running free Minecraft servers known as Aternos suffered a data breach that impacted 1.4 million subscribers.The data included usernames, email and IP addresses and hashed passwords.Compromised data: Email addresses, IP addresses, Passwords, Usernames, Website activity Avast In May 2014, the Avast anti-virus forum was hacked and 423k member records were exposed.The Simple Machines Based forum included usernames, emails and password hashes.Compromised data: Email addresses, Passwords, Usernames Badoo In June 2016, a data breach allegedly originating from the social website Badoo was found to be circulating amongst traders.

Likely obtained several years earlier, the data contained 112 million unique email addresses with personal data including names, birthdates and passwords stored as MD5 hashes.Whilst there are many indicators suggesting Badoo did indeed suffer a data breach, the legitimacy of the data could not be emphatically proven so this breach has been categorised as "unverified".Compromised data: Dates of birth, Email addresses, Genders, Names, Passwords, Usernames Battlefield Heroes In June 2011 as part of a final breached data dump, the hacker collective "LulzSec" obtained and released over half a million usernames and passwords from the game Battlefield Heroes.The passwords were stored as MD5 hashes with no salt and many were easily converted back to their plain text versions.Compromised data: Passwords, Usernames Beautiful People In November 2015, the dating website Beautiful People was hacked and over 1.1M accounts were leaked.The data was being traded in underground circles and included a huge amount of personal information related to dating.

Compromised data: Beauty ratings, Car ownership statuses, Dates of birth, Drinking habits, Education levels, Email addresses, Genders, Geographic locations, Home ownership statuses, Income levels, IP addresses, Job titles, Names, Passwords, Personal descriptions, Personal interests, Physical attributes, Sexual orientations, Smoking habits, Website activity Bell (2014 breach) In February 2014, Bell Canada suffered a data breach via the hacker collective known as NullCrew.The breach included data from multiple locations within Bell and exposed email addresses, usernames, user preferences and a number of unencrypted passwords and credit card data from 40,000 records containing just over 20,000 unique email addresses and usernames.Compromised data: Credit cards, Genders, Passwords, Usernames Bell (2017 breach) In May 2017, the Bell telecommunications company in Canada suffered a data breach resulting in the exposure of millions of customer records.The data was consequently leaked online with a message from the attacker stating that they were "releasing a significant portion of Bell.ca's data due to the fact that they have failed to cooperate with us" and included a threat to leak more.

The impacted data included over 2 million unique email addresses and 153k survey results dating back to 2011 and 2012.There were also 162 Bell employee records with more comprehensive personal data including names, phone numbers and plain text "passcodes".Bell suffered another breach in 2014 which exposed 40k records.Compromised data: Email addresses, Geographic locations, IP addresses, Job titles, Names, Passwords, Phone numbers, Spoken languages, Survey results, Usernames BigMoneyJobs was hacked by an attacker known as "ProbablyOnion".The attack resulted in the exposure of over 36,000 user accounts including email addresses, usernames and passwords which were stored in plain text.The attack was allegedly mounted by exploiting a SQL injection vulnerability.Compromised data: Career levels, Education levels, Email addresses, Names, Passwords, Phone numbers, Physical addresses, Salutations, User website URLs, Website activity Bitcoin Security Forum Gmail Dump In September 2014, a large dump of nearly 5M usernames and passwords was posted to a Russian Bitcoin forum.

Whilst the origin of the breach remains unclear, the breached credentials were confirmed by multiple source as correct, albeit a number of years old.Compromised data: Email addresses, Passwords Bitcoin Talk In May 2015, the Bitcoin forum Bitcoin Talk was hacked and over 500k unique email addresses were exposed.The attack led to the exposure of a raft of personal data including usernames, email and IP addresses, genders, birth dates, security questions and MD5 hashes of their answers plus hashes of the passwords themselves.Compromised data: Dates of birth, Email addresses, Genders, IP addresses, Passwords, Security questions and answers, Usernames, Website activity BitTorrent In January 2016, the forum for the popular torrent software BitTorrent was hacked.The IP.Board based forum stored passwords as weak SHA1 salted hashes and the breached data also included usernames, email and IP addresses.Compromised data: Email addresses, IP addresses, Passwords, Usernames Black Hat World In June 2014, the search engine optimisation forum Black Hat World had three quarters of a million accounts breached from their system.

The breach included various personally identifiable attributes which were publicly released in a MySQL database script.Compromised data: Dates of birth, Email addresses, Instant messenger identities, IP addresses, Passwords, Usernames, Website activity Bot of Legends In November 2014, the forum for Bot of Legends suffered a data breach.The IP.Board forum contained 238k accounts including usernames, email and IP addresses and passwords stored as salted MD5 hashes.Compromised data: Email addresses, IP addresses, Passwords, Usernames, Website activity Boxee In March 2014, the home theatre PC software maker Boxee had their forums compromised in an attack.The attackers obtained the entire vBulletin MySQL database and promptly posted it for download on the Boxee forum itself.The data included 160k users, password histories, private messages and a variety of other data exposed across nearly 200 publicly exposed tables.Compromised data: Dates of birth, Email addresses, Geographic locations, Historical passwords, Instant messenger identities, IP addresses, Passwords, Private messages, User website URLs, Usernames Brazzers In April 2013, the adult website known as Brazzers was hacked and 790k accounts were exposed publicly.

Each record included a username, email address and password stored in plain text.The breach was brought to light by the Vigilante.pw data breach reporting site in September 2016.Compromised data: Email addresses, Passwords, Usernames BTC-E In October 2014, the Bitcoin exchange BTC-E was hacked and 568k accounts were exposed.The data included email and IP addresses, wallet balances and hashed passwords.Compromised data: Account balances, Email addresses, IP addresses, Passwords, Usernames, Website activity Business Acumen Magazine In April 2014, the Australian "Business Acumen Magazine" website was hacked by an attacker known as 1337MiR.The breach resulted in over 26,000 accounts being exposed including usernames, email addresses and password stored with a weak cryptographic hashing algorithm (MD5 with no salt).Compromised data: Email addresses, Names, Passwords, Usernames, Website activity was breached and leaked publicly.Whilst there has been no public attribution of the breach, the leaked data included over 227k accounts and nearly 10k private messages between users of the forum.

Compromised data: Dates of birth, Email addresses, Geographic locations, Historical passwords, Instant messenger identities, IP addresses, Passwords, Private messages, Usernames, Website activity CD Projekt RED In March 2016, Polish game developer CD Projekt RED suffered a data breach.The hack of their forum led to the exposure of almost 1.9 million accounts along with usernames, email addresses and salted SHA1 passwords.Compromised data: Email addresses, Passwords, Usernames suffered a data breach.The database from the IP.Board based forum contained 445k accounts including usernames, email and IP addresses and salted MD5 password hashes.Compromised data: Email addresses, IP addresses, Passwords, Usernames Civil Online In mid-2011, data was allegedly obtained from the Chinese engineering website known as Civil Online and contained 7.8M accounts.The data in the breach contains email and IP addresses, user names and MD5 password hashes.Compromised data: Email addresses, IP addresses, Passwords, Usernames, Website activity ClixSense In September 2016, the paid-to-click site ClixSense suffered a data breach which exposed 2.4 million subscriber identities.
The breached data was then posted online by the attackers who claimed it was a subset of a larger data breach totalling 6.6 million records.The leaked data was extensive and included names, physical, email and IP addresses, genders and birth dates, account balances and passwords stored as plain text.Compromised data: Account balances, Dates of birth, Email addresses, Genders, IP addresses, Names, Passwords, Payment histories, Payment methods, Physical addresses, Usernames, Website activity CloudPets In January, the maker of teddy bears that record children's voices and sends them to family and friends via the internet CloudPets left their database publicly exposed and it was subsequently downloaded by external parties (the data was also subject to 3 different ransom demands).583k records were provided to HIBP via a data trader and included email addresses and bcrypt hashes, but the full extent of user data exposed by the system was over 821k records and also included children's names and references to portrait photos and voice recordings.

Compromised data: Email addresses, Family members' names, Passwords Comcast In November 2015, the US internet and cable TV provider Comcast suffered a data breach that exposed 590k customer email addresses and plain text passwords.A further 27k accounts appeared with home addresses with the entire data set being sold on underground forums.Compromised data: Email addresses, Passwords, Physical addresses COMELEC (Philippines Voters) In March 2016, the Philippines Commission of Elections website (COMELEC) was attacked and defaced, allegedly by Anonymous Philippines.Shortly after, data on 55 million Filipino voters was leaked publicly and included sensitive information such as genders, marital statuses, height and weight and biometric fingerprint data.The breach only included 228k email addresses.Compromised data: Biometric data, Dates of birth, Email addresses, Family members' names, Genders, Job titles, Marital statuses, Names, Passport numbers, Phone numbers, Physical addresses, Physical attributes Crack Community In late 2013, the Crack Community forum specialising in cracks for games was compromised and over 19k accounts published online.

Built on the MyBB forum platform, the compromised data included email addresses, IP addresses and salted MD5 passwords.Compromised data: Email addresses, IP addresses, Passwords, Usernames, Website activity CrimeAgency vBulletin Hacks In January 2016, a large number of unpatched vBulletin forums were compromised by an actor known as "CrimeAgency".A total of 140 forums had data including usernames, email addresses and passwords (predominantly stored as salted MD5 hashes), extracted and then distributed.Refer to the complete list of the forums for further information on which sites were impacted.Compromised data: Email addresses, Passwords, Usernames Cross Fire ) .The vBulletin forum contained 12.8 million accounts including usernames, email addresses and passwords stored as salted MD5 hashes.Compromised data: Email addresses, Passwords, Usernames DaFont In May 2017, font sharing site DaFont suffered a data breach resulting in the exposure of 637k records.Allegedly due to a SQL injection vulnerability exploited by multiple parties, the exposed data included usernames, email addresses and passwords stored as MD5 without a salt.

Compromised data: Email addresses, Passwords, Usernames DaniWeb In late 2015, the technology and social site DaniWeb suffered a data breach.The attack resulted in the disclosure of 1.1 million accounts including email and IP addresses which were also accompanied by salted MD5 hashes of passwords.However, DaniWeb have advised that "the breached password hashes and salts are incorrect" and that they have since switched to new infrastructure and software.Compromised data: Email addresses, IP addresses, Passwords Data Enrichment Records In December 2016, more than 200 million "data enrichment profiles" were found for sale on the darknet.The seller claimed the data was sourced from Experian and whilst that claim was rejected by the company, the data itself was found to be legitimate suggesting it may have been sourced from other legitimate locations.In total, there were more than 8 million unique email addresses in the data which also contained a raft of other personal attributes including credit ratings, home ownership status, family structure and other fields described in the story linked to above.

The email addresses alone were provided to HIBP.Compromised data: Buying preferences, Charitable donations, Credit status information, Dates of birth, Email addresses, Family structure, Financial investments, Home ownership statuses, Income levels, Job titles, Marital statuses, Names, Net worths, Phone numbers, Physical addresses, Political donations DLH.net In July 2016, the gaming news site DLH.net suffered a data breach which exposed 3.3M subscriber identities.Along with the keys used to redeem and activate games on the Steam platform, the breach also resulted in the exposure of email addresses, birth dates and salted MD5 password hashes.The data was donated to Have I been pwned by data breach monitoring service Vigilante.pw.Compromised data: Dates of birth, Email addresses, Names, Passwords, Usernames, Website activity and contained 8.7M accounts.The data in the breach contains email addresses and user names.Compromised data: Email addresses, Usernames Domino's In June 2014, Domino's Pizza in France and Belgium was hacked by a group going by the name "Rex Mundi" and their customer data held to ransom.

Domino's refused to pay the ransom and six months later, the attackers released the data along with troves of other hacked accounts.Amongst the customer data was passwords stored with a weak MD5 hashing algorithm and no salt.Compromised data: Email addresses, Names, Passwords, Phone numbers, Physical addresses Dropbox In mid-2012, Dropbox suffered a data breach which exposed the stored credentials of tens of millions of their customers.In August 2016, they forced password resets for customers they believed may be at risk.A large volume of data totalling over 68 million records was subsequently traded online and included email addresses and salted hashes of passwords (half of them SHA1, half of them bcrypt).Compromised data: Email addresses, Passwords Dungeons & Dragons Online In April 2013, the interactive video game Dungeons & Dragons Online suffered a data breach that exposed almost 1.6M players' accounts.The data was being actively traded on underground forums and included email addresses, birth dates and password hashes.

Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames, Website activity and contained 2.6M accounts.The data in the breach contains email addresses, user names and plain text passwords.Compromised data: Email addresses, Passwords, Usernames Edmodo In May 2017, the education platform Edmodo was hacked resulting in the exposure of 77 million records comprised of over 43 million unique customer email addresses.The data was consequently published to a popular hacking forum and made freely available.The records in the breach included usernames, email addresses and bcrypt hashes of passwords.Compromised data: Email addresses, Passwords, Usernames Elance Sometime in 2009, staffing platform Elance suffered a data breach that impacted 1.3 million accounts.Appearing online 8 years later, the data contained usernames, email addresses, phone numbers and SHA1 hashes of passwords, amongst other personal data.Compromised data: Email addresses, Employers, Geographic locations, Passwords, Phone numbers, Usernames Epic Games In August 2016, the Epic Games forum suffered a data breach, allegedly due to a SQL injection vulnerability in vBulletin.

The attack resulted in the exposure of 252k accounts including usernames, email addresses and salted MD5 hashes of passwords.Compromised data: Email addresses, Passwords, Usernames Eroticy In mid-2016, it's alleged that the adult website known as Eroticy was hacked.Almost 1.4 million unique accounts were found circulating in late 2016 which contained a raft of personal information ranging from email addresses to phone numbers to plain text passwords.Whilst many HIBP subscribers confirmed their data was legitimate, the actual source of the breach remains inconclusive.A detailed account of the data has been published in the hope of identifying the origin of the breach.Compromised data: Email addresses, IP addresses, Names, Passwords, Payment histories, Phone numbers, Physical addresses, Usernames, Website activity eThekwini Municipality In September 2016, the new eThekwini eServices website in South Africa was launched with a number of security holes that lead to the leak of over 98k residents' personal information and utility bills across 82k unique email addresses.

Emails were sent prior to launch containing passwords in plain text and the site allowed anyone to download utility bills without sufficient authentication.Various methods of customer data enumeration was possible and phishing attacks began appearing the day after launch.Compromised data: Dates of birth, Deceased date, Email addresses, Genders, Government issued IDs, Names, Passport numbers, Passwords, Phone numbers, Physical addresses, Utility bills Ethereum In December 2016, the forum for the public blockchain-based distributed computing platform Ethereum suffered a data breach.The database contained over 16k unique email addresses along with IP addresses, private forum messages and (mostly) bcrypt hashed passwords.Ethereum elected to self-submit the data to HIBP, providing the service with a list of email addresses impacted by the incident.Compromised data: Email addresses, IP addresses, Passwords, Private messages, Usernames, Website activity Evony In June 2016, the online multiplayer game Evony was hacked and over 29 million unique accounts were exposed.

The attack led to the exposure of usernames, email and IP addresses and MD5 hashes of passwords (without salt).Compromised data: Email addresses, IP addresses, Passwords, Usernames Experian In September 2015, the US based credit bureau and consumer data broker Experian suffered a data breach that impacted 15 million customers who had applied for financing from T-Mobile.An alleged data breach was subsequently circulated containing personal information including names, physical and email addresses, birth dates and various other personal attributes.Multiple Have I been pwned subscribers verified portions of the data as being accurate, but the actual source of it was inconclusive therefor this breach has been flagged as "unverified".Compromised data: Credit status information, Dates of birth, Email addresses, Ethnicities, Family structure, Genders, Home ownership statuses, Income levels, IP addresses, Names, Phone numbers, Physical addresses, Purchasing habits Exploit.In In late 2016, a huge list of email address and password pairs appeared in a "combo list" referred to as "Exploit.In".

The list contained 593 million unique email addresses, many with multiple different passwords hacked from various online systems.Compromised data: Email addresses, Passwords FashionFantasyGame In late 2016, the fashion gaming website Fashion Fantasy Game suffered a data breach.The incident exposed 2.3 million unique user accounts and corresponding MD5 password hashes with no salt.The data was contributed to Have I been pwned courtesy of rip@creep.im.Compromised data: Email addresses, Passwords Final Fantasy Shrine In September 2015, the Final Fantasy discussion forum known as FFShrine was breached and the data dumped publicly.Approximately 620k records were released containing email addresses, IP addresses and salted hashes of passwords.Compromised data: Email addresses, Passwords, Usernames, Website activity Flash Flash Revolution In February 2016, the music-based rhythm game known as Flash Flash Revolution was hacked and 1.8M accounts were exposed.Along with email and IP addresses, the vBulletin forum also exposed salted MD5 password hashes.

Compromised data: Email addresses, Passwords, Usernames Flashback In February 2015, the Swedish forum known as Flashback had sensitive internal data on 40k members published via the tabloid newspaper Aftonbladet.The data was allegedly sold to them via Researchgruppen (The Research Group) who have a history of exposing otherwise anonymous users, primarily those who they believe participate in "troll like" behaviour.The compromised data includes social security numbers, home and email addresses.Compromised data: Email addresses, Government issued IDs, Physical addresses Fling In 2011, the self-proclaimed "World's Best Adult Social Network" website known as Fling was hacked and more than 40 million accounts obtained by the attacker.The breached data included highly sensitive personal attributes such as sexual orientation and sexual interests as well as email addresses and passwords stored in plain text.Compromised data: Dates of birth, Email addresses, Genders, Geographic locations, IP addresses, Passwords, Phone numbers, Sexual fetishes, Sexual orientations, Usernames, Website activity Forbes In February 2014, the Forbes website succumbed to an attack that leaked over 1 million user accounts.

The attack was attributed to the Syrian Electronic Army, allegedly as retribution for a perceived "Hate of Syria".Compromised data: Email addresses, Passwords, User website URLs, Usernames Foxy Bingo In April 2007, the online gambling site Foxy Bingo was hacked and 252,000 accounts were obtained by the hackers.The breached records were subsequently sold and traded and included personal information data such as plain text passwords, birth dates and home addresses.Compromised data: Account balances, Browser user agent details, Dates of birth, Email addresses, Genders, Names, Passwords, Phone numbers, Physical addresses, Usernames, Website activity Freedom Hosting II In January 2017, the free hidden service host Freedom Hosting II suffered a data breach.The attack allegedly took down 20% of dark web sites running behind Tor hidden services with the attacker claiming that of the 10,613 impacted sites, more than 50% of the content was child pornography.The hack led to the exposure of MySQL databases for the sites which included a vast amount of information on the hidden services Freedom Hosting II was managing.

The impacted data classes far exceeds those listed for the breach and differ between the thousands of impacted sites.Compromised data: Email addresses, Passwords, Usernames Fridae In May 2014, over 25,000 user accounts were breached from the Asian lesbian, gay, bisexual and transgender website known as "Fridae".The attack which was announced on Twitter appears to have been orchestrated by Deletesec who claim that "Digital weapons shall annihilate all secrecy within governments and corporations".The exposed data included password stored in plain text.Compromised data: Email addresses, Passwords, Usernames, Website activity Funimation In July 2016, the anime site Funimation suffered a data breach that impacted 2.5 million accounts.The data contained usernames, email addresses, dates of birth and salted SHA1 hashes of passwords.Compromised data: Dates of birth, Email addresses, Passwords, Usernames Fur Affinity In May 2016, the Fur Affinity website for people with an interest in anthropomorphic animal characters (also known as "furries") was hacked.
The attack exposed 1.2M email addresses (many accounts had a different "first" and "last" email against them) and hashed passwords.Compromised data: Email addresses, Passwords, Usernames Gamerzplanet In approximately October 2015, the online gaming forum known as Gamerzplanet was hacked and more than 1.2M accounts were exposed.The vBulletin forum included IP addresses and passwords stored as salted hashes using a weak implementation enabling many to be rapidly cracked.Compromised data: Email addresses, IP addresses, Passwords, Usernames GameTuts Likely in early 2015, the video game website GameTuts suffered a data breach and over 2 million user accounts were exposed.The site later shut down in July 2016 but was identified as having been hosted on a vBulletin forum.The exposed data included usernames, email and IP addresses and salted MD5 hashes.Compromised data: Email addresses, IP addresses, Passwords, Usernames Gamigo In March 2012, the German online game publisher Gamigo was hacked and more than 8 million accounts publicly leaked.

The breach included email addresses and passwords stored as weak MD5 hashes with no salt.Compromised data: Email addresses, Passwords Gawker In December 2010, Gawker was attacked by the hacker collective "Gnosis" in retaliation for what was reported to be a feud between Gawker and 4Chan.Information about Gawkers 1.3M users was published along with the data from Gawker's other web presences including Gizmodo and Lifehacker.Due to the prevalence of password reuse, many victims of the breach then had their Twitter accounts compromised to send Acai berry spam.Compromised data: Email addresses, Passwords, Usernames GeekedIn In August 2016, the technology recruitment site GeekedIn left a MongoDB database exposed and over 8M records were extracted by an unknown third party.The breached data was originally scraped from GitHub in violation of their terms of use and contained information exposed in public profiles, including over 1 million members' email addresses.Full details on the incident (including how impacted members can see their leaked data) are covered in the blog post on 8 million GitHub profiles were leaked from GeekedIn's MongoDB - here's how to see yours.

Compromised data: Email addresses, Geographic locations, Names, Professional skills, Usernames, Years of professional experience GFAN In October 2016, data surfaced that was allegedly obtained from the Chinese website known as GFAN and contained 22.5M accounts.The data in the breach contains email and IP addresses, user names and salted and hashed passwords.Compromised data: Email addresses, IP addresses, Passwords, Usernames gPotato In July 2007, the multiplayer game portal known as gPotato (link to archive of the site at that time) suffered a data breach and over 2 million user accounts were exposed.The site later merged into the Webzen portal where the original accounts still exist today.The exposed data included usernames, email and IP addresses, MD5 hashes and personal attributes such as gender, birth date, physical address and security questions and answers stored in plain text.Compromised data: Dates of birth, Email addresses, Genders, IP addresses, Names, Passwords, Physical addresses, Security questions and answers, Usernames, Website activity GTAGaming In August 2016, the Grand Theft Auto forum GTAGaming was hacked and nearly 200k user accounts were leaked.

The vBulletin based forum included usernames, email addresses and password hashes.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames, Website activity hackforums.net In June 2011, the hacktivist group known as "LulzSec" leaked one final large data breach they titled "50 days of lulz".The compromised data came from sources such as AT&T, Battlefield Heroes and the hackforums.net website.The leaked Hack Forums data included credentials and personal information of nearly 200,000 registered forum users.Compromised data: Dates of birth, Email addresses, Instant messenger identities, IP addresses, Passwords, Social connections, Spoken languages, Time zones, User website URLs, Usernames, Website activity Hacking Team In July 2015, the Italian security firm Hacking Team suffered a major data breach that resulted in over 400GB of their data being posted online via a torrent.The data searchable on "Have I been pwned?"is from 189GB worth of PST mail folders in the dump.

The contents of the PST files is searchable on Wikileaks.Compromised data: Email addresses, Email messages Health Now Networks In March 2017, the telemarketing service Health Now Networks left a database containing hundreds of thousands of medical records exposed.There were over 900,000 records in total containing significant volumes of personal information including names, dates of birth, various medical conditions and operator notes on the individuals' health.The data included over 320k unique email addresses.Compromised data: Dates of birth, Email addresses, Genders, Health insurance information, IP addresses, Names, Personal health data, Phone numbers, Physical addresses, Security questions and answers, Social connections Hemmakväll In July 2015, the Swedish video store chain Hemmakväll was hacked and nearly 50k records dumped publicly.The disclosed data included various attributes of their customers including email and physical addresses, names and phone numbers.

Passwords were also leaked, stored with a weak MD5 hashing algorithm.Compromised data: Email addresses, Names, Passwords, Phone numbers, Physical addresses was hacked by a collective calling themselves "Team Appunity".The attack exposed over 28,000 usernames and email addresses along with nicknames, gender, year of birth and unsalted MD5 password hashes.Compromised data: Email addresses, Genders, Nicknames, Passwords, Usernames, Years of birth Heroes of Gaia In early 2013, the online fantasy multiplayer game Heroes of Gaia suffered a data breach.The newest records in the data set indicate a breach date of 4 January 2013 and include usernames, IP and email addresses but no passwords.Compromised data: Browser user agent details, Email addresses, IP addresses, Usernames, Website activity Heroes of Newerth In December 2012, the multiplayer online battle arena game known as Heroes of Newerth was hacked and over 8 million accounts extracted from the system.The compromised data included usernames, email addresses and passwords.

Compromised data: Email addresses, Passwords, Usernames HLTV In June 2016, the "home of competitive Counter Strike" website HLTV was hacked and 611k accounts were exposed.The attack led to the exposure of names, usernames, email addresses and bcrypt hashes of passwords.Compromised data: Email addresses, Names, Passwords, Usernames, Website activity HongFire In March 2015, the anime and manga forum HongFire suffered a data breach.The hack of their vBulletin forum led to the exposure of 1 million accounts along with email and IP addresses, usernames, dates of birth and salted MD5 passwords.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames i-Dressup In June 2016, the teen social site known as i-Dressup was hacked and over 2 million user accounts were exposed.At the time the hack was reported, the i-Dressup operators were not contactable and the underlying SQL injection flaw remained open, allegedly exposing a total of 5.5 million accounts.

The breach included email addresses and passwords stored in plain text.Compromised data: Email addresses, Passwords iMesh In September 2013, the media and file sharing client known as iMesh was hacked and approximately 50M accounts were exposed.The data was later put up for sale on a dark market website in mid-2016 and included email and IP addresses, usernames and salted MD5 hashes.Compromised data: Email addresses, IP addresses, Passwords, Usernames Insanelyi In July 2014, the iOS forum Insanelyi was hacked by an attacker known as Kim Jong-Cracks.A popular source of information for users of jailbroken iOS devices running Cydia, the Insanelyi breach disclosed over 104k users' emails addresses, user names and weakly hashed passwords (salted MD5).Compromised data: Email addresses, Passwords, Usernames, Website activity InterPals In late 2015, the online penpal site InterPals had their website hacked and 3.4 million accounts exposed.The compromised data included email addresses, geographical locations, birthdates and salted hashes of passwords.

Compromised data: Dates of birth, Email addresses, Geographic locations, Names, Passwords, Usernames iPmart During 2015, the iPmart forum (now known as Mobi NUKE) was hacked and over 2 million forum members' details were exposed.The vBulletin forum included IP addresses, birth dates and passwords stored as salted hashes using a weak implementation enabling many to be rapidly cracked.A further 368k accounts were added to "Have I been pwned" in March 2016 bringing the total to over 2.4M.Compromised data: Dates of birth, Email addresses, Passwords, Usernames began circulating in approximately September 2016.Comprised of over 24 million records, the data contained various personal attributes such as email addresses, dates of birth and physical locations.Compromised data: Dates of birth, Email addresses, Geographic locations, Names Kimsufi In mid-2015, the forum for the providers of affordable dedicated servers known as Kimsufi suffered a data breach.The vBulletin forum contained over half a million accounts including usernames, email and IP addresses and passwords stored as salted MD5 hashes.

Compromised data: Email addresses, IP addresses, Passwords, Usernames was the target of an attack which was consequently detailed on Reddit. was one of several Russian sites in the breach and impacted almost 1.5M accounts including sensitive personal information.Compromised data: Dates of birth, Email addresses, Genders, Geographic locations, Recovery email addresses, Security questions and answers, Usernames Last.fm In March 2012, the music website Last.fm was hacked and 43 million user accounts were exposed.Whilst Last.fm knew of an incident back in 2012, the scale of the hack was not known until the data was released publicly in September 2016.The breach included 37 million unique email addresses, usernames and passwords stored as unsalted MD5 hashes.Compromised data: Email addresses, Passwords, Usernames, Website activity Leet In August 2016, the service for creating and running Pocket Minecraft edition servers known as Leet was reported as having suffered a data breach that impacted 6 million subscribers.

The incident reported by Softpedia had allegedly taken place earlier in the year, although the data set sent to HIBP was dated as recently as early September but contained only 2 million subscribers.The data included usernames, email and IP addresses and SHA512 hashes.A further 3 million accounts were obtained and added to HIBP several days after the initial data was loaded bringing the total to over 5 million.Compromised data: Email addresses, IP addresses, Passwords, Usernames, Website activity Lifeboat In January 2016, the Minecraft community known as Lifeboat was hacked and more than 7 million accounts leaked.Lifeboat knew of the incident for three months before the breach was made public but elected not to advise customers.The leaked data included usernames, email addresses and passwords stored as straight MD5 hashes.Compromised data: Email addresses, Passwords, Usernames LinkedIn In May 2016, LinkedIn had 164 million email addresses and passwords exposed.Originally hacked in 2012, the data remained out of sight until being offered for sale on a dark market site 4 years later.

The passwords in the breach were stored as SHA1 hashes without salt, the vast majority of which were quickly cracked in the days following the release of the data.Compromised data: Email addresses, Passwords Linux Mint In February 2016, the website for the Linux distro known as Linux Mint was hacked and the ISO infected with a backdoor.The site also ran a phpBB forum which was subsequently put up for sale complete with almost 145k email addresses, passwords and other personal subscriber information.Compromised data: Avatars, Dates of birth, Email addresses, Geographic locations, IP addresses, Passwords, Time zones, Website activity Little Monsters In approximately January 2017, the Lady Gaga fan site known as "Little Monsters" suffered a data breach that impacted 1 million accounts.The data contained usernames, email addresses, dates of birth and bcrypt hashes of passwords.Compromised data: Dates of birth, Email addresses, Passwords, Usernames Lizard Squad In January 2015, the hacker collective known as "Lizard Squad" created a DDoS service by the name of "Lizard Stresser" which could be procured to mount attacks against online targets.

Shortly thereafter, the service suffered a data breach which resulted in the public disclosure of over 13k user accounts including passwords stored in plain text.Compromised data: Email addresses, Passwords, Usernames Lookbook In August 2012, the fashion site Lookbook suffered a data breach.The data later appeared listed for sale in June 2016 and included 1.1 million usernames, email and IP addresses, birth dates and plain text passwords.Compromised data: Dates of birth, Email addresses, IP addresses, Names, Passwords, Usernames, Website activity Lord of the Rings Online In August 2013, the interactive video game Lord of the Rings Online suffered a data breach that exposed over 1.1M players' accounts.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames, Website activity Lounge Board At some point in 2013, 45k accounts were breached from the Lounge Board "General Discussion Forum" and then dumped publicly.Lounge Board was a MyBB forum launched in 2012 and discontinued in mid 2013 (the last activity in the logs was from August 2013).

Compromised data: Email addresses, IP addresses, Names, Passwords, Private messages, Usernames, Website activity Mac-Torrents In October 2015, the torrent site Mac-Torrents was hacked and almost 94k usernames, email addresses and passwords were leaked.The passwords were hashed with MD5 and no salt.Compromised data: Email addresses, Passwords, Usernames Dump domain., the credentials were confirmed by many as legitimate for other services they had subscribed to.Compromised data: Email addresses, Passwords MajorGeeks In November 2015, almost 270k accounts from the MajorGeeks support forum were breached.The accounts were being actively sold and traded online and included email addresses, salted password hashes and IP addresses.Compromised data: Email addresses, IP addresses, Passwords, Usernames Malwarebytes In November 2014, the Malwarebytes forum was hacked and 111k member records were exposed.The IP.Board forum included email and IP addresses, birth dates and passwords stored as salted hashes using a weak implementation enabling many to be rapidly cracked.

Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames, Website activity Manga Traders had the usernames and passwords of over 900k users leaked on the internet (approximately 855k of the emails were unique).The passwords were weakly hashed with a single iteration of MD5 leaving them vulnerable to being easily cracked.Compromised data: Email addresses, Passwords suffered a huge data breach resulting in the disclosure of over 27 million subscribers' information.The data included deeply personal information about their private lives including drug and alcohol habits, incomes levels and sexual fetishes as well as passwords stored in plain text.Compromised data: Astrological signs, Dates of birth, Drinking habits, Drug habits, Education levels, Email addresses, Ethnicities, Fitness levels, Genders, Geographic locations, Income levels, Job titles, Names, Parenting plans, Passwords, Personal descriptions, Physical attributes, Political views, Relationship statuses, Religions, Sexual fetishes, Travel habits, Usernames, Website activity, Work habits Minecraft Pocket Edition Forum In May 2015, the Minecraft Pocket Edition forum was hacked and over 16k accounts were dumped public.

Allegedly hacked by @rmsg0d, the forum data included numerous personal pieces of data for each user.The forum has subsequently been decommissioned.Compromised data: Email addresses, IP addresses, Passwords, Usernames Minecraft World Map In approximately January 2016, the Minecraft World Map site designed for sharing maps created for the game was hacked and over 71k user accounts were exposed.The data included usernames, email and IP addresses along with salted and hashed passwords.Compromised data: Email addresses, IP addresses, Passwords, Usernames Minefield In June 2015, the French Minecraft server known as Minefield was hacked and 188k member records were exposed.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames, Website activity MoDaCo In approximately January 2016, the UK based Android community known as MoDaCo suffered a data breach which exposed 880k subscriber identities.The data included email and IP addresses, usernames and passwords stored as salted MD5 hashes.

Compromised data: Email addresses, IP addresses, Passwords, Usernames Modern Business Solutions In October 2016, a large Mongo DB file containing tens of millions of accounts was shared publicly on Twitter (the file has since been removed).The database contained over 58M unique email addresses along with IP addresses, names, home addresses, genders, job titles, dates of birth and phone numbers.The data was subsequently attributed to "Modern Business Solutions", a company that provides data storage and database hosting solutions.They've yet to acknowledge the incident or explain how they came to be in possession of the data.Compromised data: Dates of birth, Email addresses, Genders, IP addresses, Job titles, Names, Phone numbers, Physical addresses Money Bookers Sometime in 2009, the e-wallet service known as Money Bookers suffered a data breach which exposed almost 4.5M customers.Now called Skrill, the breach was not discovered until October 2015 and included names, email addresses, home addresses and IP addresses.

Compromised data: Dates of birth, Email addresses, IP addresses, Names, Phone numbers, Physical addresses MPGH In October 2015, the multiplayer game hacking website MPGH was hacked and 3.1 million user accounts disclosed.The vBulletin forum breach contained usernames, email addresses, IP addresses and salted hashes of passwords.Compromised data: Email addresses, IP addresses, Passwords, Usernames MrExcel In December 2016, the forum for the Microsoft Excel tips and solutions site Mr Excel suffered a data breach.The hack of the vBulletin forum led to the exposure of over 366k accounts along with email and IP addresses, dates of birth and salted passwords hashed with MD5.The owner of the MrExcel forum subsequently self-submitted the data to HIBP.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Social connections, Usernames, Website activity mSpy In May 2015, the "monitoring" software known as mSpy suffered a major data breach.The software (allegedly often used to spy on unsuspecting victims), stored extensive personal information within their online service which after being breached, was made freely available on the internet.

Compromised data: Device usage tracking data Muslim Directory In February 2014, the UK guide to services and business known as the Muslim Directory was attacked by the hacker known as @th3inf1d3l.The data was consequently dumped publicly and included the web accounts of tens of thousands of users which contained data including their names, home address, age group, email, website activity and password in plain text.Compromised data: Age groups, Email addresses, Employers, Names, Passwords, Phone numbers, Physical addresses, Website activity Muslim Match In June 2016, the Muslim Match dating website had 150k email addresses exposed.The data included private chats and messages between relationship seekers and numerous other personal attributes including passwords hashed with MD5.Compromised data: Chat logs, Email addresses, Geographic locations, IP addresses, Passwords, Private messages, User statuses, Usernames myRepoSpace In July 2015, the Cydia repository known as myRepoSpace was hacked and user data leaked publicly.

Cydia is designed to facilitate the installation of apps on jailbroken iOS devices.The repository service was allegedly hacked by @its_not_herpes and 0x8badfl00d in retaliation for the service refusing to remove pirated tweaks.Compromised data: Email addresses, IP addresses, Passwords, Usernames MySpace In approximately 2008, MySpace suffered a data breach that exposed almost 360 million accounts.In May 2016 the data was offered up for sale on the "Real Deal" dark market website and included email addresses, usernames and SHA1 hashes of the first 10 characters of the password converted to lowercase and stored without a salt.The exact breach date is unknown, but analysis of the data suggests it was 8 years before being made public.Compromised data: Email addresses, Passwords, Usernames MyVidster In August 2015, the social video sharing and bookmarking site MyVidster was hacked and nearly 20,000 accounts were dumped online.The dump included usernames, email addresses and hashed passwords.

Compromised data: Email addresses, Passwords, Usernames Naughty America In March 2016, the adult website Naughty America was hacked and the data consequently sold online.The breach included data from numerous systems with various personal identity attributes, the largest of which had passwords stored as easily crackable MD5 hashes.There were 1.4 million unique email addresses in the breach.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames, Website activity Neopets In May 2016, a set of breached data originating from the virtual pet website "Neopets" was found being traded online.Allegedly hacked "several years earlier", the data contains sensitive personal information including birthdates, genders and names as well as almost 27 million unique email addresses.Passwords were stored in plain text and IP addresses were also present in the breach.Compromised data: Dates of birth, Email addresses, Genders, Geographic locations, IP addresses, Names, Passwords, Usernames NetEase ) was reported as having suffered a data breach that impacted hundreds of millions of subscribers.

Whilst there is evidence that the data itself is legitimate (multiple HIBP subscribers confirmed a password they use is in the data), due to the difficulty of emphatically verifying the Chinese breach it has been flagged as "unverified".Compromised data: Email addresses, Passwords Neteller In May 2010, the e-wallet service known as Neteller suffered a data breach which exposed over 3.6M customers.The breach was not discovered until October 2015 and included names, email addresses, home addresses and account balances.Compromised data: Account balances, Dates of birth, Email addresses, Genders, IP addresses, Names, Phone numbers, Physical addresses, Security questions and answers, Website activity NetProspex In 2016, a list of over 33 million individuals in corporate America sourced from Dun & Bradstreet's NetProspex service was leaked online.D&B believe the targeted marketing data was lost by a customer who purchased it from them.It contained extensive personal and corporate information including names, email addresses, job titles and general information about the employer.

Compromised data: Email addresses, Employers, Job titles, Names, Phone numbers, Physical addresses NextGenUpdate Early in 2014, the video game website NextGenUpdate reportedly suffered a data breach that disclosed almost 1.2 million accounts.Amongst the data breach was usernames, email addresses, IP addresses and salted and hashed passwords.Compromised data: Email addresses, IP addresses, Passwords, Usernames Nexus Mods In December 2015, the game modding site Nexus Mods released a statement notifying users that they had been hacked.They subsequently dated the hack as having occurred in July 2013 although there is evidence to suggest the data was being traded months in advance of that.The breach contained usernames, email addresses and passwords stored as a salted hashes.Compromised data: Email addresses, Passwords, Usernames Nihonomaru In late 2015, the anime community known as Nihonomaru had their vBulletin forum hacked and 1.7 million accounts exposed.The compromised data included email and IP addresses, usernames and salted hashes of passwords.

Compromised data: Email addresses, IP addresses, Passwords, Usernames Nival In February 2016, the Russian gaming company Nival was the target of an attack which was consequently detailed on Reddit.Allegedly protesting "the foreign policy of Russia in regards to Ukraine", Nival was one of several Russian sites in the breach and impacted over 1.5M accounts including sensitive personal information.Compromised data: Avatars, Dates of birth, Email addresses, Genders, Names, Spoken languages, Usernames, Website activity Non Nude Girls In May 2013, the non-consensual voyeurism site "Non Nude Girls" suffered a data breach.The hack of the vBulletin forum led to the exposure of over 75k accounts along with email and IP addresses, names and plain text passwords.Compromised data: Email addresses, IP addresses, Names, Passwords, Usernames, Website activity Nulled In May 2016, the cracking community forum known as Nulled was hacked and 599k user accounts were leaked publicly.

The compromised data included email and IP addresses, weak salted MD5 password hashes and hundreds of thousands of private messages between members.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Private messages, Usernames, Website activity Onverse In January 2016, the online virtual world known as Onverse was hacked and 800k accounts were exposed.Along with email and IP addresses, the site also exposed salted MD5 password hashes.Compromised data: Email addresses, IP addresses, Passwords, Usernames OVH In mid-2015, the forum for the hosting provider known as OVH suffered a data breach.The vBulletin forum contained 453k accounts including usernames, email and IP addresses and passwords stored as salted MD5 hashes.Compromised data: Email addresses, IP addresses, Passwords, Usernames OwnedCore In approximately August 2013, the World of Warcraft exploits forum known as OwnedCore was hacked and more than 880k accounts were exposed.Compromised data: Email addresses, IP addresses, Passwords, Usernames Paddy Power In October 2010, the Irish bookmaker Paddy Power suffered a data breach that exposed 750,000 customer records with nearly 600,000 unique email addresses.

The breach was not disclosed until July 2014 and contained extensive personal information including names, addresses, phone numbers and plain text security questions and answers.Compromised data: Account balances, Dates of birth, Email addresses, IP addresses, Names, Phone numbers, Physical addresses, Security questions and answers, Usernames, Website activity Patreon In October 2015, the crowdfunding site Patreon was hacked and over 16GB of data was released publicly.The dump included almost 14GB of database records with more than 2.3M unique email addresses and millions of personal messages.Compromised data: Email addresses, Payment histories, Physical addresses, Private messages, Website activity PayAsUGym In December 2016, an attacker breached PayAsUGym's website exposing over 400k customers' personal data.The data was consequently leaked publicly and broadly distributed via Twitter.The leaked data contained personal information including email addresses and passwords hashed using MD5 without a salt.

Compromised data: Browser user agent details, Email addresses, IP addresses, Names, Partial credit card data, Passwords, Phone numbers, Website activity PHP Freaks In October 2015, the PHP discussion board PHP Freaks was hacked and 173k user accounts were publicly leaked.The breach included multiple personal data attributes as well as salted and hashed passwords.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames, Website activity Pixel Federation In December 2013, a breach of the web-based game community based in Slovakia exposed over 38,000 accounts which were promptly posted online.The breach included email addresses and unsalted MD5 hashed passwords, many of which were easily converted back to plain text.Compromised data: Email addresses, Passwords Plex In July 2015, the discussion forum for Plex media centre was hacked and over 327k accounts exposed.The IP.Board forum included IP addresses and passwords stored as salted hashes using a weak implementation enabling many to be rapidly cracked.

Compromised data: Email addresses, IP addresses, Passwords, Usernames Pokébip In July 2015, the French Pokémon site Pokébip suffered a data breach which exposed 657k subscriber identities.The data included email and IP addresses, usernames and passwords stored as unsalted MD5 hashes.Compromised data: Email addresses, IP addresses, Passwords, Time zones, Usernames, Website activity Pokémon Creed In August 2014, the Pokémon RPG website Pokémon Creed was hacked after a dispute with rival site, Pokémon Dusk.In a post on Facebook, "Cruz Dusk" announced the hack then pasted the dumped MySQL database on pkmndusk.in.The breached data included over 116k usernames, email addresses and plain text passwords.Compromised data: Email addresses, Genders, IP addresses, Passwords, Usernames, Website activity Pokémon Negro In approximately October 2016, the Spanish Pokémon site Pokémon Negro suffered a data breach.The attack resulted in the disclosure of 830k accounts including email and IP addresses along with plain text passwords.

Pokémon Negro did not respond when contacted about the breach.Compromised data: Email addresses, IP addresses, Passwords PS3Hax In approximately July 2015, the Sony Playstation hacks and mods forum known as PS3Hax was hacked and more than 447k accounts were exposed.Compromised data: Email addresses, IP addresses, Passwords, Usernames PSP ISO In approximately September 2015, the PlayStation PSP forum known as PSP ISO was hacked and almost 1.3 million accounts were exposed.Compromised data: Email addresses, IP addresses, Passwords, Usernames PSX-Scene In approximately February 2015, the Sony Playstation forum known as PSX-Scene was hacked and more than 340k accounts were exposed.Compromised data: Email addresses, IP addresses, Passwords, Usernames Qatar National Bank In July 2015, the Qatar National Bank suffered a data breach which exposed 15k documents totalling 1.4GB and detailing more than 100k accounts with passwords and PINs.The incident was made public some 9 months later in April 2016 when the documents appeared publicly on a file sharing site.

Analysis of the breached data suggests the attack began by exploiting a SQL injection flaw in the bank's website.Compromised data: Bank account numbers, Banking PINs, Customer feedback, Dates of birth, Financial transactions, Genders, Geographic locations, Government issued IDs, IP addresses, Marital statuses, Names, Passwords, Phone numbers, Physical addresses, Security questions and answers, Spoken languages QIP In mid-2011, the Russian instant messaging service known as QIP (Quiet Internet Pager) suffered a data breach.The attack resulted in the disclosure of over 26 million unique accounts including email addresses and passwords with the data eventually appearing in public years later.Compromised data: Email addresses, Passwords, Usernames, Website activity Quantum Booter In March 2014, the booter service Quantum Booter (also referred to as Quantum Stresser) suffered a breach which lead to the disclosure of their internal database.The leaked data included private discussions relating to malicious activity Quantum Booter users were performing against online adversaries, including the IP addresses of those using the service to mount DDoS attacks.

Compromised data: Email addresses, IP addresses, Passwords, Private messages, Usernames, Website activity QuinStreet In approximately late 2015, the maker of "performance marketing products" QuinStreet had a number of their online assets compromised., (view a full list of sites).QuinStreet advised that impacted users have been notified and passwords reset.The data contained details on over 4.9 million people and included email addresses, dates of birth and salted MD5 hashes.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames, Website activity R2 (2017 forum breach) In early 2017, the forum for the gaming website R2 Games was hacked.R2 had previously appeared on HIBP in 2015 after a prior incident.This one exposed over 1 million unique user accounts and corresponding MD5 password hashes with no salt.Compromised data: Email addresses, Passwords, Usernames, Website activity R2Games In late 2015, the gaming website R2Games was hacked and more than 2.1M personal records disclosed.

A further 11M accounts were added to "Have I been pwned" in March 2016 and another 9M in July 2016 bringing the total to over 22M.Compromised data: Email addresses, IP addresses, Passwords, Usernames Rambler In late 2016, a data dump of almost 100M accounts from Rambler, sometimes referred to as "The Russian Yahoo", was discovered being traded online.The data set provided to Have I been pwned included 91M unique usernames (which also form part of Rambler email addresses) and plain text passwords.According to Rambler, the data dates back to March 2014.Compromised data: Email addresses, Passwords, Usernames Regpack In July 2016, a tweet was posted with a link to an alleged data breach of BlueSnap, a global payment gateway and merchant account provider.The data contained 324k payment records across 105k unique email addresses and included personal attributes such as name, home address and phone number.The data was verified with multiple Have I been pwned subscribers who confirmed it also contained valid transactions, partial credit card numbers, expiry dates and CVVs.

A downstream consumer of BlueSnap services known as Regpack was subsequently identified as the source of the data after they identified human error had left the transactions exposed on a publicly facing server.A full investigation of the data and statement by Regpack is detailed in the post titled Someone just lost 324k payment records, complete with CVVs.Compromised data: Browser user agent details, Credit card CVV, Email addresses, IP addresses, Names, Partial credit card data, Phone numbers, Physical addresses, Purchases Retina-X In February 2017, the mobile device monitoring software developer Retina-X was hacked and customer data downloaded before being wiped from their servers.The incident was covered in the Motherboard article titled Inside the 'Stalkerware' Surveillance Market, Where Ordinary People Tap Each Other's Phones.The service, used to monitor mobile devices, had 71k email addresses and MD5 hashes with no salt exposed.Retina-X disclosed the incident in a blog post on April 27, 2017.

Compromised data: Email addresses, Passwords River City Media Spam List In January 2017, a massive trove of data from River City Media was found exposed online.The data was found to contain almost 1.4 billion records including email and IP addresses, names and physical addresses, all of which was used as part of an enormous spam operation.Once de-duplicated, there were 393 million unique email addresses within the exposed data.Compromised data: Email addresses, IP addresses, Names, Physical addresses Rosebutt Board Some time prior to May 2016, the forum known as "Rosebutt Board" was hacked and 107k accounts were exposed.The self-described "top one board for anal fisting, prolapse, huge insertions and rosebutt fans" had email and IP addresses, usernames and weakly stored salted MD5 password hashes hacked from the IP.Board based forum.Compromised data: Email addresses, IP addresses, Passwords, Usernames SC Daily Phone Spam List In early 2015, a spam list known as SC Daily Phone emerged containing almost 33M identities.

The data includes personal attributes such as names, physical and IP addresses, genders, birth dates and phone numbers.Read more about spam lists in HIBP.Compromised data: Dates of birth, Email addresses, Genders, IP addresses, Names, Physical addresses Seedpeer In July 2015, the torrent site Seedpeer was hacked and 282k member records were exposed.The data included usernames, email addresses and passwords stored as weak MD5 hashes.Compromised data: Email addresses, Passwords, Usernames ServerPact In mid-2015, the Dutch Minecraft site ServerPact was hacked and 73k accounts were exposed.Along with birth dates, email and IP addresses, the site also exposed SHA1 password hashes with the username as the salt.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames SkTorrent In February 2016, the Slovak torrent tracking site SkTorrent was hacked and over 117k records leaked online.The data dump included usernames, email addresses and passwords stored in plain text.

Compromised data: Email addresses, Passwords, Usernames Snapchat In January 2014 just one week after Gibson Security detailed vulnerabilities in the service, Snapchat had 4.6 million usernames and phone number exposed.The attack involved brute force enumeration of a large number of phone numbers against the Snapchat API in what appears to be a response to Snapchat's assertion that such an attack was "theoretical".Consequently, the breach enabled individual usernames (which are often used across other services) to be resolved to phone numbers which users usually wish to keep private.Compromised data: Geographic locations, Phone numbers, Usernames Sony In 2011, Sony suffered breach after breach after breach — it was a very bad year for them.The breaches spanned various areas of the business ranging from the PlayStation network all the way through to the motion picture arm, Sony Pictures. lead to tens of thousands of accounts across multiple systems being exposed complete with plain text passwords.

Compromised data: Dates of birth, Email addresses, Genders, Names, Passwords, Phone numbers, Physical addresses, Usernames Soundwave In approximately mid 2015, the music tracking app Soundwave suffered a data breach.The breach stemmed from an incident whereby "production data had been used to populate the test database" and was then inadvertently exposed in a MongoDB.The data contained 130k records and included email addresses, dates of birth, genders and MD5 hashes of passwords without a salt.Compromised data: Dates of birth, Email addresses, Genders, Geographic locations, Names, Passwords, Social connections Special K Data Feed Spam List In mid to late 2015, a spam list known as the Special K Data Feed was discovered containing almost 31M identities.Compromised data: Dates of birth, Email addresses, Genders, IP addresses, Names, Physical addresses Spirol In February 2014, Connecticut based Spirol Fastening Solutions suffered a data breach that exposed over 70,000 customer records.

The attack was allegedly mounted by exploiting a SQL injection vulnerability which yielded data from Spirol’s CRM system ranging from customers’ names, companies, contact information and over 55,000 unique email addresses.Compromised data: Email addresses, Employers, Job titles, Names, Phone numbers, Physical addresses StarNet In February 2015, the Moldavian ISP "StarNet" had it's database published online.The dump included nearly 140k email addresses, many with personal details including contact information, usage patterns of the ISP and even passport numbers.Compromised data: Customer interactions, Dates of birth, Email addresses, Genders, IP addresses, MAC addresses, Names, Passport numbers, Passwords, Phone numbers Ster-Kinekor In 2016, the South African cinema company Ster-Kinekor had a security flaw which leaked a large amount of customer data via an enumeration vulnerability in the API of their old website.Whilst more than 6 million accounts were leaked by the flaw, the exposed data only contained 1.6 million unique email addresses.

The data also included extensive personal information such as names, addresses, birthdates, genders and plain text passwords.Compromised data: Dates of birth, Email addresses, Genders, Names, Passwords, Phone numbers, Physical addresses, Spoken languages Stratfor In December 2011, "Anonymous" attacked the global intelligence company known as "Stratfor" and consequently disclosed a veritable treasure trove of data including hundreds of gigabytes of email and tens of thousands of credit card details which were promptly used by the attackers to make charitable donations (among other uses).The breach also included 860,000 user accounts complete with email address, time zone, some internal system data and MD5 hashed passwords with no salt.Compromised data: Credit cards, Email addresses, Names, Passwords, Phone numbers, Physical addresses, Usernames Sumo Torrent In June 2014, the torrent site Sumo Torrent was hacked and 285k member records were exposed.The data included IP addresses, email addresses and passwords stored as weak MD5 hashes.

Compromised data: Email addresses, IP addresses, Passwords, Usernames, Website activity In July 2015, the Swedish tech news site SweClockers was hacked and 255k accounts were exposed.The attack led to the exposure of usernames, email addresses and salted hashes of passwords stored with a combination of MD5 and SHA512.Compromised data: Email addresses, Passwords, Usernames Taobao In approximately 2012, it's alleged that the Chinese shopping site known as Taobao suffered a data breach that impacted over 21 million subscribers.Compromised data: Email addresses, Passwords Team SoloMid In December 2014, the electronic sports organisation known as Team SoloMid was hacked and 442k members accounts were leaked.The accounts included email and IP addresses, usernames and salted hashes of passwords.Compromised data: Email addresses, IP addresses, Passwords, Usernames Telecom Regulatory Authority of India In April 2015, the Telecom Regulatory Authority of India (TRAI) published tens of thousand of emails sent by Indian citizens supporting net neutrality as part of the SaveTheInternet campaign.

The published data included lists of emails including the sender's name and email address as well as the contents of the email as well, often with signatures including other personal data.Compromised data: Email addresses, Email messages Teracod In May 2015, almost 100k user records were extracted from the Hungarian torrent site known as Teracod.The data was later discovered being torrented itself and included email addresses, passwords, private messages between members and the peering history of IP addresses using the service.Compromised data: Avatars, Email addresses, IP addresses, Passwords, Payment histories, Private messages, Usernames, Website activity Tesco In February 2014, over 2,000 Tesco accounts with usernames, passwords and loyalty card balances appeared on Pastebin.Whilst the source of the breach is not clear, many confirmed the credentials were valid for Tesco and indeed they have a history of poor online security.Compromised data: Email addresses, Passwords, Reward program balances The Candid Board In September 2015, the non-consensual voyeurism site "The Candid Board" suffered a data breach.

The hack of the vBulletin forum led to the exposure of over 178k accounts along with email and IP addresses, dates of birth and salted passwords hashed with MD5.Compromised data: Dates of birth, Email addresses, Geographic locations, IP addresses, Passwords, Usernames, Website activity The Fappening In December 2015, the forum for discussing naked celebrity photos known as "The Fappening" (named after the iCloud leaks of 2014) was compromised and 179k accounts were leaked.Exposed member data included usernames, email addresses and salted hashes of passwords.Compromised data: Email addresses, Passwords, Usernames ThisHabbo Forum , a Finnish social networking site) appeared among a list of compromised sites which has subsequently been removed from the internet.Whilst the actual date of the exploit is not clear, the breached data includes usernames, email addresses, IP addresses and salted hashes of passwords.A further 584k records were added from a more comprehensive breach file provided in October 2016.

Compromised data: Email addresses, IP addresses, Passwords, Usernames Tianya In December 2011, China's largest online forum known as Tianya was hacked and tens of millions of accounts were obtained by the attacker.The leaked data included names, usernames and email addresses.Compromised data: Email addresses, Names, Usernames Torrent Invites In December 2013, the torrent site Torrent Invites was hacked and over 352k accounts were exposed.The vBulletin forum contained usernames, email and IP addresses, birth dates and salted MD5 hashes of passwords.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames, Website activity Trillian In December 2015, the instant messaging application Trillian suffered a data breach.The breach became known in July 2016 and exposed various personal data attributes including names, email addresses and passwords stored as salted MD5 hashes.Compromised data: Dates of birth, Email addresses, IP addresses, Names, Passwords, Usernames TruckersMP In February 2016, the online trucking simulator mod TruckersMP suffered a data breach which exposed 84k user accounts.

In a first for "Have I been pwned", the breached data was self-submitted directly by the organisation that was breached itself.Compromised data: Email addresses, Passwords, Usernames tumblr In early 2013, tumblr suffered a data breach which resulted in the exposure of over 65 million accounts.The data was later put up for sale on a dark market website and included email addresses and passwords stored as salted SHA1 hashes.Compromised data: Email addresses, Passwords Uiggy In June 2016, the Facebook application known as Uiggy was hacked and 4.3M accounts were exposed, 2.7M of which had email addresses against them.The leaked accounts also exposed names, genders and the Facebook ID of the owners.Compromised data: Email addresses, Genders, Names, Social connections, Website activity UN Internet Governance Forum In February 2014, the Internet Governance Forum (formed by the United Nations for policy dialogue on issues of internet governance) was attacked by hacker collective known as Deletesec.

Although tasked with "ensuring the security and stability of the Internet", the IGF’s website was still breached and resulted in the leak of 3,200 email addresses, names, usernames and cryptographically stored passwords.Compromised data: Email addresses, Names, Passwords, Usernames Unreal Engine In August 2016, the Unreal Engine Forum suffered a data breach, allegedly due to a SQL injection vulnerability in vBulletin.The attack resulted in the exposure of 530k accounts including usernames, email addresses and salted MD5 hashes of passwords.Compromised data: Email addresses, Passwords, Usernames uTorrent In early 2016, the forum for the uTorrent BitTorrent client suffered a data breach which came to light later in the year.The database from the IP.Board based forum contained 395k accounts including usernames, email addresses and MD5 password hashes without a salt.Compromised data: Email addresses, Passwords, Usernames uuu9 and contained 7.5M accounts.Compromised data: Email addresses, Passwords, Usernames vBulletin In November 2015, the forum software maker vBulletin suffered a serious data breach.

The attack lead to the release of both forum user and customer accounts totalling almost 519k records.The breach included email addresses, birth dates, security questions and answers for customers and salted hashes of passwords for both sources.Compromised data: Dates of birth, Email addresses, Homepage URLs, Instant messenger identities, IP addresses, Passwords, Security questions and answers, Spoken languages, Website activity Verified In January 2014, one of the largest communities of Eastern Europe cybercriminals known as "Verified" was hacked.The breach exposed nearly 17k users of the vBulletin forum including their personal messages and other potentially personally identifiable information.Compromised data: Email addresses, Historical passwords, IP addresses, Passwords, Private messages, Usernames, Website activity VINs In June 2017, an unsecured database with more than 10 million VINs (vehicle identification numbers) was discovered by researchers.Believed to be sourced from US car dealerships, the data included a raft of personal information and vehicle data along with 397k unique email addresses.

Compromised data: Dates of birth, Email addresses, Family structure, Genders, Names, Phone numbers, Physical addresses, Vehicle details VK In approximately 2012, the Russian social media site known as VK was hacked and almost 100 million accounts were exposed.The data emerged in June 2016 where it was being sold via a dark market website and included names, phone numbers email addresses and plain text passwords.Compromised data: Email addresses, Names, Passwords, Phone numbers Vodafone In November 2013, Vodafone in Iceland suffered an attack attributed to the Turkish hacker collective "Maxn3y".The data was consequently publicly exposed and included user names, email addresses, social security numbers, SMS message, server logs and passwords from a variety of different internal sources.Compromised data: Credit cards, Email addresses, Government issued IDs, IP addresses, Names, Passwords, Phone numbers, Physical addresses, Purchases, SMS messages, Usernames VTech In November 2015, hackers extracted more than 4.8 million parents' and 227k children's accounts from VTech's Learning Lodge website.

The Hong Kong company produces learning products for children including software sold via the compromised website.The data breach exposed extensive personal details including home addresses, security questions and answers and passwords stored as weak MD5 hashes.Furthermore, children's details including names, ages, genders and associations to their parents' records were also exposed.Compromised data: Dates of birth, Email addresses, Family members' names, Genders, IP addresses, Names, Passwords, Physical addresses, Security questions and answers, Usernames, Website activity War Inc.In mid-2012, the real-time strategy game War Inc.suffered a data breach.The attack resulted in the exposure of over 1 million accounts including usernames, email addresses and salted MD5 hashes of passwords.Compromised data: Email addresses, Passwords, Usernames, Website activity Warframe In November 2014, the online game Warframe was hacked and 819k unique email addresses were exposed.Allegedly due to a SQL injection flaw in Drupal, the attack exposed usernames, email addresses and data in a "pass" column which adheres to the salted SHA12 password hashing pattern used by Drupal 7.

Digital Extremes (the developers of Warframe), asserts the salted hashes are of "alias names" rather than passwords.Compromised data: Email addresses, Usernames, Website activity WHMCS In May 2012, the web hosting, billing and automation company WHMCS suffered a data breach that exposed 134k email addresses.The breach included extensive information about customers and payment histories including partial credit card numbers.Compromised data: Email addresses, Email messages, Employers, IP addresses, Names, Partial credit card data, Passwords, Payment histories, Physical addresses, Website activity WIIU ISO In September 2015, the Nintendo Wii U forum known as WIIU ISO was hacked and 458k accounts were exposed.Compromised data: Email addresses, IP addresses, Passwords, Usernames WildStar In July 2015, the IP.Board forum for the gaming website WildStar suffered a data breach that exposed over 738k forum members' accounts.Compromised data: Dates of birth, Email addresses, IP addresses, Passwords, Usernames Win7Vista Forum In September 2013, the Win7Vista Windows forum (since renamed to the "Beyond Windows 9" forum) was hacked and later had its internal database dumped.

The dump included over 200k members’ personal information and other internal data extracted from the forum.Compromised data: Email addresses, Instant messenger identities, IP addresses, Names, Passwords, Private messages, Usernames, Website activity Wishbone In August 2016, the mobile app to "compare anything" known as Wishbone suffered a data breach.The data contained 9.4 million records with 2.2 million unique email addresses and was allegedly a subset of the complete data set.The exposed data included genders, birthdates, email addresses and phone numbers for an audience predominantly composed of teenagers and young adults.Compromised data: Auth tokens, Dates of birth, Email addresses, Genders, Names, Phone numbers, Usernames WPT Amateur Poker League In January 2014, the World Poker Tour (WPT) Amateur Poker League website was hacked by the Twitter user @smitt3nz.The attack resulted in the public disclosure of 175,000 accounts including 148,000 email addresses.The plain text password for each account was also included in the breach.

Compromised data: Email addresses, Passwords xat In November 2015, the online chatroom known as "xat" was hacked and 6 million user accounts were exposed.Used as a chat engine on websites, the leaked data included usernames, email and IP addresses along with hashed passwords.Compromised data: Email addresses, IP addresses, Passwords, Usernames, Website activity Xbox 360 ISO In approximately September 2015, the XBOX 360 forum known as XBOX360 ISO was hacked and 1.2 million accounts were exposed.Compromised data: Email addresses, IP addresses, Passwords, Usernames Xbox-Scene In approximately February 2015, the Xbox forum known as Xbox-Scene was hacked and more than 432k accounts were exposed.Compromised data: Email addresses, IP addresses, Passwords, Usernames XSplit In November 2013, the makers of gaming live streaming and recording software XSplit was compromised in an online attack.The data breach leaked almost 3M names, email addresses, usernames and hashed passwords.

Compromised data: Email addresses, Names, Passwords, Usernames Yahoo In July 2012, Yahoo!had their online publishing service "Voices" compromised via a SQL injection attack.The breach resulted in the disclosure of nearly half a million usernames and passwords stored in plain text.The breach showed that of the compromised accounts, a staggering 59% of people who also had accounts in the Sony breach reused their passwords across both services.Compromised data: Email addresses, Passwords Yandex Dump In September 2014, news broke of a massive leak of accounts from Yandex, the Russian search engine giants who also provides email services. accounts with both companies claiming the credentials were acquired via phishing scams rather than being obtained as a result of direct attacks against their services.Compromised data: Email addresses, Passwords Youku In late 2016, the online Chinese video service Youku suffered a data breach.The incident exposed 92 million unique user accounts and corresponding MD5 password hashes.

Compromised data: Email addresses, Passwords YouPorn In February 2012, the adult website YouPorn had over 1.3M user accounts exposed in a data breach.The publicly released data included both email addresses and plain text passwords.Credit to squeal.net for providing the data breach.Compromised data: Email addresses, Passwords Zoosk In approximately 2011, an alleged breach of the dating website Zoosk began circulating.Comprised of almost 53 million records, the data contained email addresses and plain text passwords.However, during extensive verification in May 2016 no evidence could be found that the data was indeed sourced from the dating service.This breach has consequently been flagged as fabricated; it's highly unlikely the data was sourced from Zoosk.Compromised data: Email addresses, Passwords Пара Па ) .The vBulletin forum contained 4.9 million accounts including usernames, email addresses and passwords stored as salted MD5 hashes.Compromised data: Email addresses, Passwords, Usernames Спрашивай.ру In May 2015, Спрашивай.ру (a the Russian website for anonymous reviews) was reported to have had 6.7 million user details exposed by a hacker known as "w0rm".